
Threats are evolving, and it’s survival of the cyber-fittest. Is your business keeping up? Use our cyber readiness scorecard to find out your level of maturity to meet today's cyber threats.
Disruptions like outages or cyberattacks can halt operations and hurt your company. A Business Continuity and Disaster Recovery (BCDR) plan helps keep things running and recover quickly. Learn how to avoid 8 common BCDR mistakes.
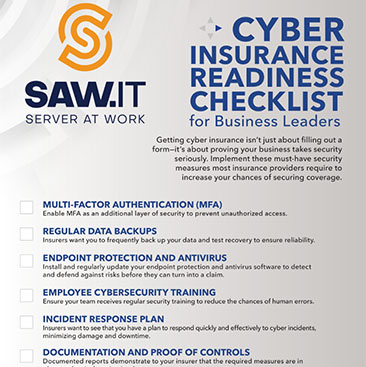
Businesses must implement key security measures like MFA, data backups, antivirus, employee training, incident response plans, and documented controls to prove readiness for cybersecurity insurance.

Use this checklist to spot a reliable IT service provider—one with proven experience, strong security, and strategic planning. Don’t risk your business on guesswork—use the right criteria to choose an IT partner who will help your business.

Your technology should be your greatest asset — not your biggest liability. Many businesses don’t realize their IT strategy is risky until it’s too late. Discover ten red flags that indicate your business IT may be putting you in jeopardy.

Cybercriminals exploit human nature with 7 social engineering tactics: phishing, spear phishing, pretexting, quid pro quo, baiting, tailgating, and watering hole attacks—each designed to trick employees into exposing sensitive data.